There are lots of posts here about how to get Azure AD SAML working with self-hosted Redash and not a lot of success. I want to give credit to these two threads on helping us get it working. What follows below is a guide on how to enable Redash SSO with SAML to Azure AD without modifying the Redash source code.
Here is an error we ran into for SEO since there wasn’t much on Google for this code:
Request Id: 9f4bcae7-dcbf-4bb8-9989-7e6f6734ab00
Correlation Id: 7bbfade4-92fe-4536-a5fd-99faf2f4ebb0
Timestamp: 2021-03-30T20:34:04Z
Message: AADSTS7500511: XML attribute 'Format' in the SAML message must be a URI.
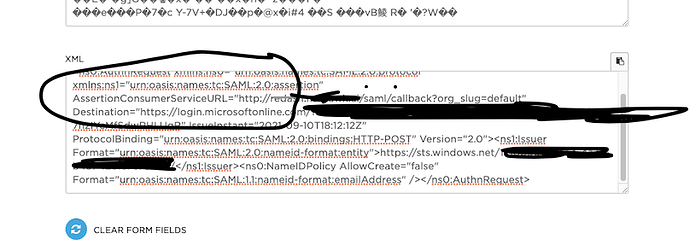
What this means is that the Format attribute of the node in the SAML message was not a URI. But in reality, it needed to be the following URN in the SAML NameID Format config in Redash:
urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress
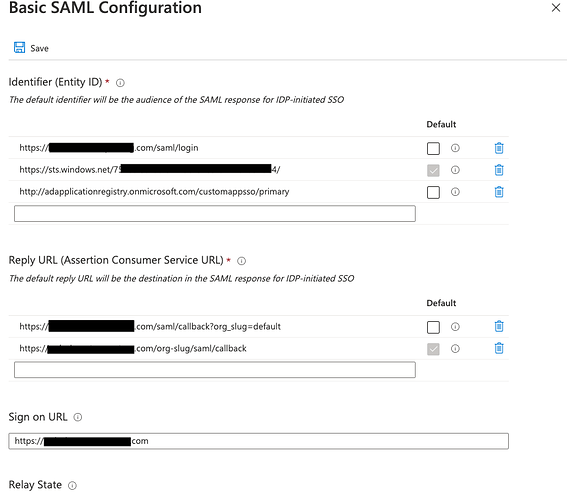
So, here are the required settings on the Azure and Redash sides:
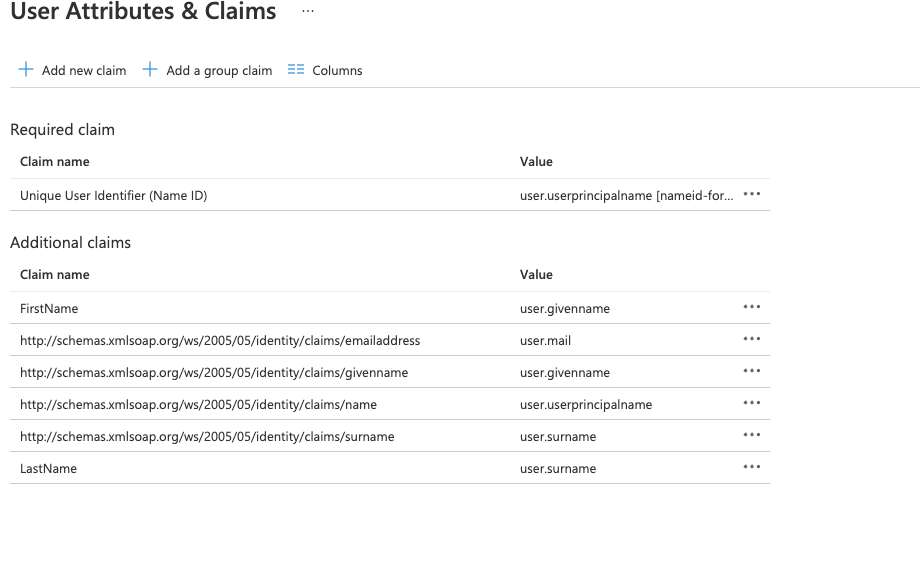
If you do not configure the claims as directed below, you will run into this error in redash/authentication/saml_auth.py’:
authn_response.ava[“FirstName”][0]
If you enable LOG_LEVEL=debug, you can look in the logs and see an output line for AVA={…} which will show all of the parameters in the AVA dictionary (this is performed by the underlying pysaml2 client which parses the authn request/response.
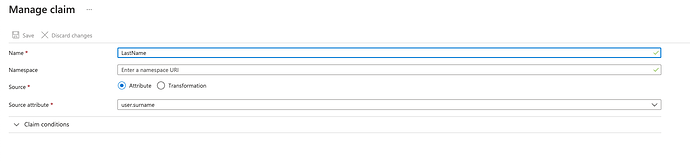
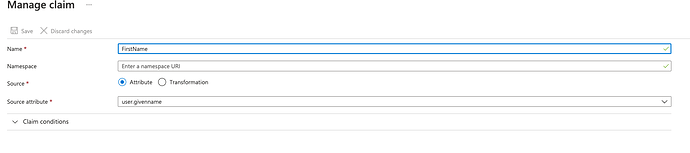
Here’s how to configure the claims to get around this:
Note that a namespace is not required. If you provide it, it will fail. Leave that field blank!
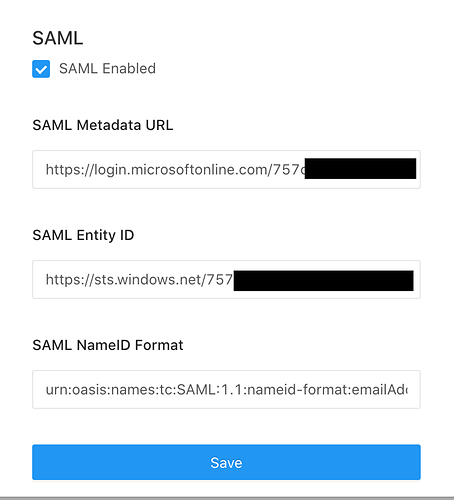
Lastly, here are the Redash settings which correspond to the Azure settings:
Again, note the urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress value that goes into NameID Format.
That should be all it takes. This was performed on Version: 8.0.0+b32245 (a16f551e) running under Docker in AWS ECS.